National Question Paper November 2012
Question 3 - Scenario
The scenario below sets the scene for the questions that follow.
The Computer Applications Technology (CAT) learners have been asked to work with Mr Joe, the teacher, to set up a new computer centre at the school. As a CAT learner, you need to assist with any computer-related problems.
Mr Joe saw the advertisement below for a notebook computer (laptop). Study the advertisement and answer the questions that follow.
| Intel Core i5 2.3 GHz 4 GB memory 750 GB hard drive 15.6" LED, GeForce GT 520M 1 GB 1.3 MP Webcam, Bluetooth, Wi-Fi + 3G, Win 7 Home Premium |
3.1 Give the speed of the processor in the advertisement.
Answer
Intel Core i5 2.3 GHz or 2.3 Ghz
3.2 A range of input devices is available for portable computers.
3.2.1 Name TWO of the most common input devices found on notebook computers that are NOT specified in the advertisement.
Answer
• Keyboard
• Pointing devices: such as touch pad/joystick
• Microphone
• Touch screen
• Finger print reader
3.2.2 State ONE advantage of using a wireless mouse as an input device for a computer.
Answer
• May free up desk space
• Reduce clutter/no cables
• Mouse can be used at a distance further away from a computer than a mouse cable would allow
3.3 Name the device described by the specification below:
GeForce GT 520M 1 GB
Answer
• Graphics/video/screen/display/3G card/graphics accelerator
3.4 State TWO functions of an operating system in a computer.
Answer
• Controls/manages the hardware (Makes the hardware work)
• Manages storage space
• Manages the allocation of memory to different processes
• Provides the user interface
• Controls/manages I/O (Input/Output)
• Controls/manages basic security
3.5 The webcam has a specification of 1.3 MP.
3.5.1 Explain what the specification 1.3 MP means.
Answer
• Maximum resolution of image
• Megapixels or image/picture element
• The quality of the image, etc.
3.5.2 State TWO uses of a webcam for the computer centre.
Answer
• Security surveillance/taking photographs for security
• VoIP/Skype usage/social communication
• Video conferencing/collaborating with other users
• Taking photographs/recording video
3.6 Name TWO cellular technology services or communication types that allow Internet access using cellphones.
Answer
• 3G/4G
• GPRS/EDGE (2.5G)
• WAP
• HSDPA/HSUPA/UMTS
• LTE
3.7 Give TWO reasons why Mr Joe may prefer to buy notebook computers rather than desktop computers for the school.
Answer
• Easy to take to a safe when not in use
• Mobility - can be used in different classrooms/places (via a wireless network)
• Can be used for a limited time if there is a power outage
• Needs less space in the computer lab/they are thin and lightweight
• Fewer cables/aesthetics
• Uses less electricity
• Easier to set up in a network
3.8 As it is expensive to set up a computer centre, the school wishes to use the computers for more than just teaching CAT and IT.
Name TWO other educational purposes for which the computers can be used.
Answer
• Internet for educational purposes – The Learning Channel, research, news, YouTube tutorial programs, etc.
(Allocate only one mark for any Internet-related answer)
• Outreach programmes - computer literacy classes for the community or training programmes, educational seminars, etc.
• Learners can use it to make a school website or run the school magazine
• Use DVD/CD-based resource material
• Computer Aided Learning (CAL)/Computer Aided Instruction (CAI) programs/reading/remedial programs/administration/
Learner Management System (LMS)/learning/assessment
• School project work
• Development of learner resources/support material by the teacher
3.9 Name ONE way in which a bar code scanner in the new computer centre could benefit the rest of the school.
Answer
• Can use it to keep record of all the laboratory equipment (in computer centres or science labs)
• Can barcode library/text books for stock records, issues and returns/Improves efficiency of issuing/Returning books/Improves the productivity/Reduces time spent (in the school library)
• Can record stock or the selling of items (in the school tuck shop)
3.10 Mr Joe is interested in exploring the accessibility options for physically challenged (disabled) learners in the classroom.
3.10.1 Explain how a speech recognition program can be used to assist physically challenged (disabled) learners. In your answer, refer to a specific problem that voice recognition will overcome.
Answer
• Learners who cannot use their hands properly can use the speech recognition program to convert speech to text, i.e. to type what he/she is saying
• Visually impaired learners can use speech recognition to give commands to the computer, etc.
• Visually impaired learners can use speech recognition to convert speech into text, etc.
3.10.2 A text-to-speech program such as Narrator is often associated with operating systems.
Name ONE way in which a text-to-speech program can be used to help learners with special needs. In your answer, refer to a specific difficulty that this will overcome.
Answer
• Example: Visually impaired users
Usage: the program will read what is on the screen
• Example: Dyslexic learners
Usage: can use it to read teaching and other materials to them
• Example: Apraxia learners (those who cannot speak)
Usage: can use it to communicate, etc.
3.11 Mr Joe was advised to install a CD drive in each computer.
3.11.1 State ONE disadvantage of fitting a CD drive in each computer.
Answer
• Takes longer to copy data to a CD than transferring data to a flash drive
• If it is only a CD-ROM reader, learners would not be able to write a CD
• The CD-drives are more expensive than flash disks
• If CD-drive is not used frequently it becomes inoperable/unusable
• CD-drives are outdated/older technology/cannot use DVDs, etc.
3.11.2 Give ONE reason, other than the larger capacity of a Blu-Ray disc, to install Blu-Ray drives as opposed to CD drives in the computers.
Answer
• Both DVD and CD formats can be used/backward compatible
• Newer technology
• Better quality
• Faster access to data
3.12 Give TWO general reasons why ergonomic issues have to be considered when setting up a computer centre. Specific examples are NOT required.
Answer
To avoid injury
To be able to work effectively/productively/improve the working environment, etc
Question 4
4.1 When Mr Joe unpacked the computers he found that an office suite had been installed on the computers already. Before the office suite can be used an activation code has to be entered.4.1.1 What is an activation code?
Answer
• Allows you to use the program
• Activates the program
• Gives access to the key/code that unlocks the security or the protection of a program,
• Is a series of numbers characters/letters
4.1.2 Where would you get an activation code?
Answer
• From software developer’s website
• From the supplier
• With the original CD/DVD set/packaging
• On the license agreement provided
4.1.3 Why do developers of software use activation codes?
Answer
• To ensure that the program is loaded only on the number of computers specified on the license
• Reduce piracy/certify that program is an original copy/increase security
4.1.4 Name the general group of software that an office suite belongs to.
Answer
Application/productivity software
4.1.5 State TWO advantages of using an office suite as opposed to individual programs from different software vendors.
Answer
• Can integrate between the different applications
• Interface is standardised across the different applications
• Functions are standardised across the programs
• Cost – cheaper to purchase an office suite
• Easier to manage updates
4.2 The office suite that was pre-loaded on the computers does not include a database program.
Motivate why Mr Joe should buy a database program by referring to a suitable example of where it can be used in the school.
Answer
To store, manipulate and maintain school and learner records
To offer CAT, etc.
4.3 When Mr Joe tried to install a printer on the computer, a message appeared that asked him to load a device driver.
4.3.1 Explain what a device driver is.
Answer
• It is software/program/utility
• That allows the printer to communicate with/be used by the operating system/computer
4.3.2 Recommend TWO ways of finding device drivers for the printer.
Answer
• Check which drivers were automatically installed from the operating system's database/load generic drivers
• Check on the CD that comes with the printer
• Download from the Internet/manufacturer's website
• Borrow a CD from someone who has the same printer,
• Obtain from a computer shop, etc.
4.4 Resources are sometimes wasted in a computer centre.
4.4.1 State TWO ways in which printing can be reduced to save paper in the computer centre.
Answer
• Use print preview before printing/edit document before printing so that you do not print unnecessary copies
• Print on both sides of the paper
• Change document formatting, for example, smaller font size/reduce margin size
• Print two or more pages to one sheet
• Save electronically/use more electronic communication/ documents
4.4.2 State TWO advantages of using less printer ink or toner in the computer centre.
Answer
• Significant cost saving/reduced cost/increased savings, etc.
• Fewer cartridges and/or less ink is produced, leads to reducing the carbon footprint/Fewer cartridges need to be disposed of
Answer
• Use energy star compliant/energy saving devices/equipment, for example, a thin client network/solar powered devices
• Switch off devices when not in use
• Set computers to sleep mode/hibernation when not in use for a while, etc.
Answer
• The antivirus program on his home computer is outdated/not updated recently
• The antivirus program on his computer was deactivated
• The license/trial period for the antivirus program has expired
• The antivirus program does not pick up a specific virus – virus is too new to be included in the virus definitions
• False-positive (incorrect reporting)
Answer
• Computer slows down/runs slower than usual
• Available memory is less than usual
• Files become corrupt/Programs or files do not work properly
• Screen displays unusual images or messages
• Music or unusual sounds play randomly
• Existing files and programs disappear
• Unknown programs or files appear
• System properties change
• Operating system does not start up
• Operating system shuts down/crashes unexpectedly, etc.
Answer
• Allow/add new functionality
• 'Bugs' (errors) are fixed/Solves problems that occurred in the program
• Better security/security loopholes can be plugged
• Modifications to device drivers are made
• Access to new expanded components such as themes are given
Answer
• A patch is downloaded (automatically from the Internet)
• From a service pack, etc.
Answer
• There has not been a lot of deleting from and writing to the hard disk/The hard drives have hardly been used
• The computers are new and the users have not yet installed and uninstalled many other programs
• It is an SSD (solid state drive)
• External hard drive
• Flash disk/card
• Blu-Ray disc
• Tape
• Triple layer DVD
Answer
Question 5
5.1 Mr Joe has networked all the computers, a scanner and other devices in the computer centre.5.1.1 Name ONE media category that Mr Joe could have used to connect the computers.
Answer
• Cable
• Wireless
5.1.2 What is the purpose of a switch in a network?
Answer
• It is a central connection point where all the devices on the network plug in
• Directs network traffic
Answer
• Printer/multifunction device
• Router/wireless router/Internet access points
• Storage drives/External hard drive
• Photocopier
5.2 Mr Joe is concerned about the security of the network.
5.2.1 State TWO precautions that he can take to prevent unauthorised access to the files on the network.
Answer
• Provide all users with passwords/encryption
• Install a firewall
• Set/restrict access rights
• Biometric device, etc.
5.2.2 State TWO guidelines for setting up secure passwords.
Answer
• Use both upper and lowercase letters
• Use a combination of numbers, letters and other characters
• Do not use easily identifiable information, for example, name, ID numbers, etc.
• Make the password longer than 8 characters
5.2.3 Name TWO problems directly related to hardware that may cause you to lose data.
Answer
• Power failure
• Power surges
• Hardware failure/disk crash
5.3 Mr Joe spends a lot of time setting up users and computers, fixing problems with computers and connectivity and performing other network tasks. He wants to advertise for someone to take over these tasks.
Give the job title (designation) that should be used in the advertisement for such a person.
Answer
Network administrator
5.4 Mr Joe wishes to connect the network to the Internet.
5.4.1 Suggest ONE type of broadband Internet connection.
(Do not give a brand name.)
Answer
• ADSL
• WiMax
• Wi-Fi
• 2.5G/3G/4G/LTE
• Satellite
5.4.2
State ONE advantage of a broadband connection for the learners in the learning environment.
Answer
• They can watch educational videos over the Internet/
educational gaming
• Faster/quicker/The downloading/uploading of data will be faster
• Permanently connected
5.5 Some teachers at the school do not believe that learners having access to the Internet is always such a good idea.
5.5.1 Other than doing research, state TWO uses of the Internet that will assist learners with their school work.
Answer
• Can ask experts questions online
• They can view tutorials on topics they are having trouble with
• Read e-books
• Watch videos/YouTube
• Play educational games
• Quizzes/Online competitions
• Online practise tests and examinations
• Blog or build own website, etc.
5.5.2 A search engine may return thousands of possible websites to look at and many of these are not relevant to what the learner is looking for.
State TWO ways in which the learner can limit the search to give only relevant websites.
Answer
• Limit the search to certain types of information, for example images or videos.
• Use specific words/phrases
• Use logical operators such as AND, OR, NOT
• Consider the word order/Put the most important words first
• Search date ranges
• Use specific domains/advanced search features
5.6 Give TWO reasons why some people store data in the 'cloud'.
Answer
• To access files on the Internet from any computer
• To allow others to access their files/collaboration
• To store off-site backups/safekeeping
• Easier to transfer larger files (e.g. ftp/Dropbox)
5.7 Mr Joe is concerned about the negative impact that the Internet may have on learners.
5.7.1 He decides to install a program that will allow him to watch what the learners do on the computers.
Give ONE ethical reason why this is a bad idea.
Answer
He is invading the privacy of the learners
Name ONE way in which he can make sure that the learners do not visit undesirable websites.
Answer
• Use security software (e.g. Netnanny)
• Proxy server/Firewall to block certain sites
• Use filters of browser program
5.8
Mr Joe wants to inform the learners about e-commerce.
5.8.1
Name TWO advantages of Internet banking over conventional banking.
Answer
• They do not have to queue at the bank/It is more convenient to do transactions online
• It is physically safer if people do not carry money on them
• Lower banking charges
• Available 24/7
(Do NOT give specific examples in your answer.)
Answer
Auction/online trading site
Answer
• You can advertise the item you wish to sell to a wider audience
• Buying or selling can take place at any time/across time-zones/convenient
• Opportunity to operate a business online
• Easy to compare prices
• Not confined by distance
• Save costs by not travelling to shops, etc.
Answer
It means that certain security measures have been taken/it is a secure site/encryption used
Answer
Digital signature
Question 6
6.1 Access to the Internet makes the school part of an online community.6.1.1 Name ONE social networking website.
Answer
• Facebook
• Flickr
• YouTube
• LinkedIn
• Twitter
• Foursquare
• Instagram
• MySpace
• Badoo
• myLife
• Google+
• Pinterest, etc.
6.1.2 Blogs and websites are also ways in which learners can communicate with people all over the world.
Is the information found on a blog less reliable than information found in an online encyclopaedia? Explain your answer.
Answer
• Yes, a blog is a personal account/journal of a point of view, experience or even research
• An online encyclopaedia is usually reviewed and checked by subject experts in the field. (In general, an online encyclopaedia is more reliable than a blog)
6.2 Some social networking websites allow one to place photographs on the Internet.
Give ONE reason why it is NOT ethical to place a photograph of someone else on a social networking website without their permission.
Answer
• It invades their privacy
• It may depict them in unflattering ways
• It may not be a true reflection of the person
6.3 Many companies use social networking.
State TWO advantages of a company using social networking.
Answer
• Reaches their clients immediately/easier to communicate with customers
• A cheaper way of marketing/advertising products/services
• Advertise/market products/services directly to a specific target audience
• Get feedback of service or products
• Access to global markets
6.4 People often use e-mail to communicate with one another.
6.4.1 State TWO disadvantages of web-based e-mail systems.
Answer
• Can only access your e-mails if you have Internet access
• Do not always have as many features as an office suite application
• May not be as fast
• May experience limited choices for creating an e-mail account
• The credibility may be questionable/more anonymous
• Could be more susceptible to spam/adverts/banners
• Mail box has a limited size
6.4.2 What do we call the set of rules that provides guidelines on how to use the Internet and e-mail in a polite and considerate way?
Answer
Netiquette
6.5 Mr Joe uses e-mail as the main method of communicating with other schools.
6.5.1 Although the area he lives in often experiences power failures, he still receives all his e-mail.
Explain why Mr Joe's e-mail is not lost during a power failure. Refer to the process whereby e-mail is sent and received.
Answer
• The e-mail service provider will keep the message in the mailbox
• until it can be transferred to Mr Joe's computer
6.5.2 Explain how Mr Joe will send an e-mail to Ms Smith without the other recipients of the message knowing that Ms Smith will also receive the e-mail.
Answer
Use the Bcc field of the e-mail program for Ms Smith
6.5.3 Explain to Mr Joe what a mailing or distribution list is in the context of e-mail communication.
Answer
A group of e-mail names and addresses given a single name
6.5.4 State ONE advantage of using a mailing or distribution list in e-mail communication.
Answer
• It saves time because all the names do not have to be typed in one at a time
• Any e-mail sent to the group will be sent to every person in the mailing list
• Prevents errors in typing an address and omission of an address
• Avoids the restriction the number of e-mail addresses that can be entered
6.6 Phishing attempts are not limited to e-mail or the Internet. They are also sent as messages to cellphones.
6.6.1 Explain in detail what a phishing attempt is and what it tries to achieve.
Answer
• It is an e-mail or message that appears to come from a trusted source, such as a bank
• To trick a person into giving personal details
• That can be used to commit fraud
6.6.2 State TWO ways in which you would recognise a message that is a phishing attempt.
Answer
• There may be spelling errors in the message
• The e-mail may be sent from a web address other than the expected one
• The message would ask you to follow a link and then to enter sensitive information
• Will ask to confirm confidential details such as passwords, etc.
• Inspect the properties of any links.
6.7 One of the teachers uses the computers to run a business during school time.
Briefly explain what makes this practice unethical.
Answer
• Using the school’s resources for own gain
• Using school time for business/steals school time
• Neglects teaching duties, etc.
6.8 Internet use is not limited to computers.
6.8.1 Name a generic type of handheld device that can be used to access the Internet.
Answer
Smartphone/PDA/tablet/e-Readers
6.8.2 Name ONE operating system used on such a handheld device.
Answer
• Symbian
• iPhone operating system
• Android (e.g. Ice Cream Sandwich/Honeycomb/Gingerbread/
JellyBean)
• Blackberry operating system
• Windows 7/8 mobile/Windows mobile
• Ubuntu for Android
• Linux (e.g. Maemo, MeeGo), etc.
6.9 Mr Joe is pleased to receive the RSS feeds he has subscribed to. 6.9.1 Explain what an RSS feed is.
Answer
Updated website content /news/sport news sent automatically from a website (pushed) usually in an e-mail with a link to the actual updated content
6.9.2 What is the main advantage of receiving an RSS feed?
Answer
It alerts you to new content without having to check the website directly
Question 7
Mr Joe has to solve several problems regarding computers and the work learners are doing in the computer centre.
7.1 One of the computers in the class has stopped responding. Explain how you would solve the problem without rebooting the computer.
Answer
• Open the task manager (use Ctrl+Alt+Delete)
• Close the program that is not responding
7.2 When the learners tried to install a new program on one of the computers, a message appeared indicating that there was not enough space left on the hard drive.
Name TWO solutions for this problem without upgrading or adding new hardware.
Answer
• Run Disk cleanup/Delete temporary files and cookies/Empty Recycle Bin
• Delete data/duplicate files from the hard drive
• Uninstall unused programs/components
• Make use of file/disk compression (zip)
7.3 The flatbed scanner connected to the network is not responding.
Name TWO things that Mr Joe can do to try and solve the problem.
Answer
• Check if the scanner is switched on
• Check that the network cable is plugged in properly
• Re-install the device driver
• Check whether the scanner is broken
7.4 Mr Joe received an e-mail message with the subject line 'Undeliverable e-mail'.
Give TWO possible reasons why this message may have appeared.
Answer
• The e-mail address he sent the message to is wrong/does not exist
• The mail server is not online
• Mailbox of recipient is full
• Attachment rejected (virus/size/content)
7.5 Mr Joe received an e-mail with an attachment that he cannot open because the computer does not recognise the type of file.
Suggest TWO ways in which to solve this problem.
Answer
• Source the original program that will open the file from the Internet/install the program that will open the file on the
computer
• Ask the sender to re-send the file in a format/version that your computer can open
• Try opening with another program, etc.
7.6 Mr Joe purchased a new version of a program. He now needs to remove the old program from his computer.
7.6.1 Give ONE reason why he should not just select the program and then press 'Delete'.
Answer
• It may not delete properly/completely
• It may delete files that will prevent other programs from working properly
• It may corrupt the system
7.6.2 Suggest ONE way in which the program can be removed without causing any problems.
Answer
• Use the uninstaller that was installed with the program
• Go to the Control Panel and then use the function to remove the program (Add/Remove / Programs and Features)
7.7 Mr Joe has asked some learners to help him in the computer centre in the afternoons.
He has created a spreadsheet to calculate the times worked by each learner.
Study the extract from the spreadsheet below and answer the questions that follow.
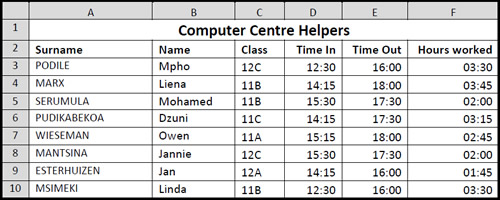
7.7.1
Mr Joe wants to copy the names of only the learners in Grade 12C.
Suggest a way in which Mr Joe can extract the names of the learners in Grade 12C without copying each name separately.
Answer
• Sort/filter the spreadsheet
• According to the class column
7.7.2 Which formatting feature did Mr Joe use to place the heading in one cell across all the columns in the first row?
Answer
• Merge
• Merge and Center
• Merge Cells (Open Office)
7.7.3 Mr Joe wishes to know how many hours each learner worked.
He used the formula =E3-D3 (Time Out minus Time In) but found that the number of hours display as a time, for example 03:30 instead of 3.5.
State TWO changes Mr Joe should make to display the number of hours correctly.
Answer
• Multiply the answer by 24 (Accept correct conversion)
• Format the cells/field to Number
7.7.4 Mr Joe needs to have the same information which appears in the spreadsheet, in a database application.
Which feature of an office package can he use to achieve this?
Answer
• Import
• Copy and paste
• Copy
7.7.5 The chart/graph below compares the times the learners have worked in the computer centre.
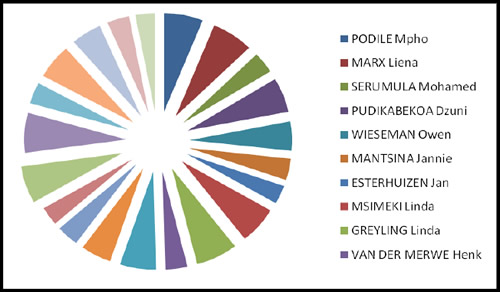
Suggest a more appropriate type of chart/graph to display and compare the data.
Answer
Column/bar chart
7.8 Mr Joe wishes to place the information below in a database table.
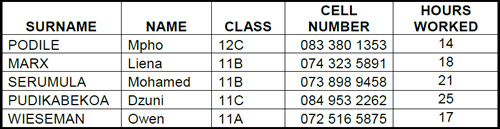
7.8.1
Which field should Mr Joe set as the primary key field?
Motivate your answer.
Answer
• Cell Number
• Each entry will be unique/prevents duplication of record
7.8.2 Learners may not work more than 30 hours. Name the field property that Mr Joe must set so that numbers larger than 30 cannot be entered into the Hours worked field.
Answer
Validation rule
7.9 The school principal requires a printed document that displays the names, surnames and hours worked of all the learners who helped in the computer centre.
7.9.1 Which database object would be most suitable to create and save a list of the learners in Grade 11B who worked more than 15 hours?
Answer
Query (or report based on a query)
7.9.2
How would you calculate and display the number of records in a database report?